Over the years, I've witnessed a transformation in the way organisations approach information securi...


Over the years, I've witnessed a transformation in the way organisations approach information securi...
Amazon Cognito User Pools are capable of issuing identity tokens in the form of JSON Web Tokens (JWT...

In the world of web development, JSON Web Tokens (JWTs) have become a popular choice for securely tr...

Performing a security audit of cloud infrastructure provides numerous benefits, ensuring the robustn...

👩💼 Senior manager: How long do you need to deliver Feature X? Software developer: That will take ...
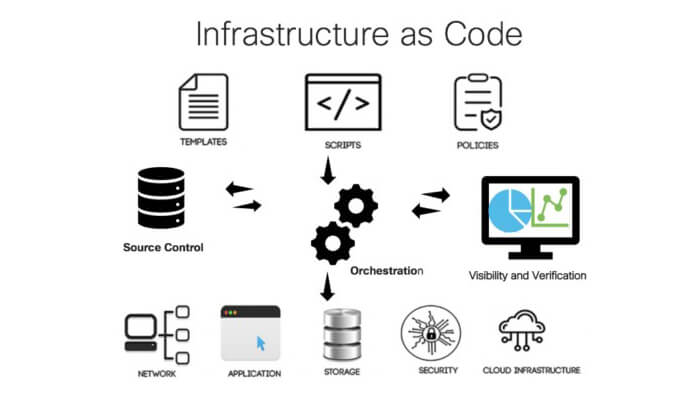
Discover the concept of infrastructure-as-code and its importance in modern IT operations.

Do you understand the emerging new standard in network security - Zero Trust Security Model? Learn h...

Does your organisation have a well-implemented and effective JML process that incorporates steps for...

The Principle of Least Privilege is about minimal access. It ensures that every part of your system ...

Explore the essential best practices for securing your cloud environment and protecting your data.